We built Vinkius because none of the existing platforms did what we needed. Not because they were bad — some of them are genuinely good at what they do. But none of them solved the full problem.
This is an honest comparison. We’ll tell you exactly where each platform excels and where it falls short. We’ll include ourselves in the same analysis. If another platform is a better fit for your use case, we’d rather you know that upfront.
What you’re actually choosing between
Every team building AI agents eventually hits the same wall: the agent needs to interact with real tools — Stripe, GitHub, Jira, Salesforce — and the integration layer is either fragile, insecure, or both.
The market has responded with several platforms, but they approach the problem from fundamentally different angles. Understanding those angles is the key to making the right choice.
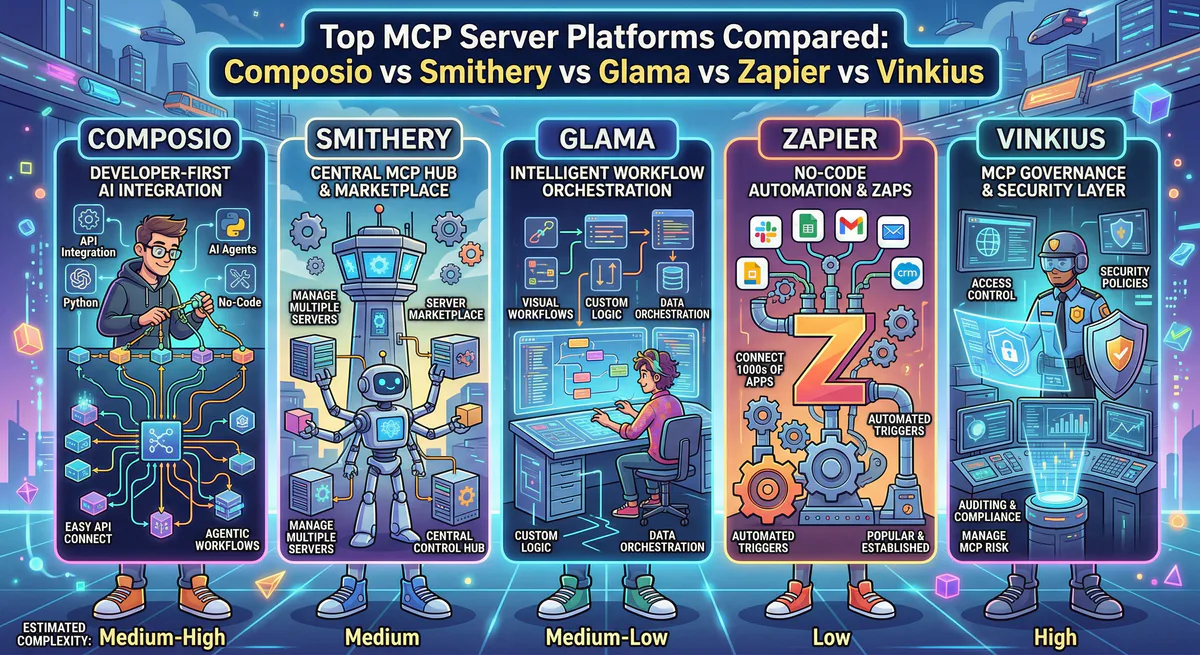
Composio
Composio is the most well-funded player in the MCP infrastructure space and positions itself as an enterprise integration platform for AI agents.
What they do well. Composio offers a large library of pre-built integrations. They handle OAuth flows, token refresh, and credential rotation, which eliminates one of the most painful parts of agent development. They achieved SOC 2 Type II and ISO 27001 certification, which matters for enterprise procurement. Their MCP Gateway provides centralized routing and API key enforcement.
Where they fall short. Composio built a tool-calling platform first and added MCP support later. The protocol is a transport layer for an existing integration engine, not a first-principles MCP runtime. Their DLP capabilities focus on prompt-level PII masking — anonymizing data before it hits the LLM. This protects the model from seeing sensitive data, but it does not prevent a compromised agent from exfiltrating data through a tool call to an external endpoint. Outbound data exfiltration — the most dangerous vector in 2026 — is an architectural blind spot when your DLP only operates on the prompt path.
Composio also does not offer a public marketplace where third-party developers can publish and monetize MCP servers. Their catalog is internally curated, which means you’re limited to the integrations their team has built.
Best for: Teams with existing Composio deployments that need broad SaaS connectivity and are comfortable delegating governance to a single vendor.
Smithery
Smithery pioneered the concept of a centralized MCP server registry. It is effectively “npm for MCP servers” — a place to discover, evaluate, and install MCP servers built by the community.
What they do well. The discovery experience is excellent. You can search by function, browse categories, and read community ratings before installing a server. Smithery supports both local (stdio) and remote (HTTP) transport, and their CLI tools make installation frictionless. For developers exploring the MCP ecosystem for the first time, Smithery is the natural starting point.
Where they fall short. Smithery is a registry, not an execution layer. It helps you find and install MCP servers, but it does not govern what those servers do once they’re running. There is no centralized credential isolation — API keys are stored locally on your machine. There is no DLP pipeline scanning outbound data. There is no audit trail beyond what the individual server implementation provides. There is no semantic classification of tool calls. And there is no marketplace with commercial licensing — developers can list servers, but cannot sell access.
For prototyping and personal use, this is fine. For production deployments where compliance, data governance, and auditability matter, Smithery leaves those responsibilities entirely to you.
Best for: Individual developers exploring MCP, prototyping agent workflows, and discovering community-built tools.
Glama
Glama positions itself as a discovery hub and managed gateway. It sits between Smithery’s pure registry model and a full execution platform.
What they do well. Glama indexes a large number of MCP servers and provides quality and security scoring to help developers evaluate options. Their managed gateway proxies tool calls through their infrastructure, which gives them a centralized point for logging, access control, and credential management. This is a meaningful step up from raw local installations.
Where they fall short. Glama’s governance capabilities are lighter than what production enterprise deployments typically require. Their gateway provides access control at the connection level, but does not offer the granular semantic classification that differentiates read-only queries from destructive mutations. They do not provide a real-time DLP pipeline that scans outbound payloads for sensitive data before they leave the perimeter. And they do not offer an open marketplace where third-party developers can publish, price, and sell MCP servers.
Best for: Teams that want a discovery experience with basic gateway governance and centralized credential management.
Zapier MCP
Zapier entered the MCP space by wrapping their massive automation library behind an MCP interface. Instead of building individual MCP servers for each tool, Zapier exposes their existing integration library as MCP-compatible tool calls.
What they do well. The breadth is unmatched. Zapier connects to thousands of applications through their existing workflow engine. If you need your agent to interact with an obscure SaaS tool that nobody has built an MCP server for, Zapier probably supports it. The no-code setup is friendly for non-developers.
Where they fall short. The MCP layer is a wrapper on top of Zapier’s existing architecture, not a native MCP runtime. Tool calls are mediated through Zapier’s infrastructure, which introduces latency and adds Zapier’s per-task pricing to every interaction. This makes high-frequency agent workflows expensive. The governance model is Zapier’s — not yours. You cannot self-host, deploy your own DLP rules, or inspect the raw execution pipeline. And the MCP interface inherits the limitations of Zapier’s action model, which was designed for short-lived, trigger-based automations rather than the stateful, multi-step workflows that modern agents require.
Best for: Teams already using Zapier that want to expose their existing automations to an AI agent without rebuilding integrations.
Vinkius
We’re including ourselves in this comparison because transparency matters more than marketing.
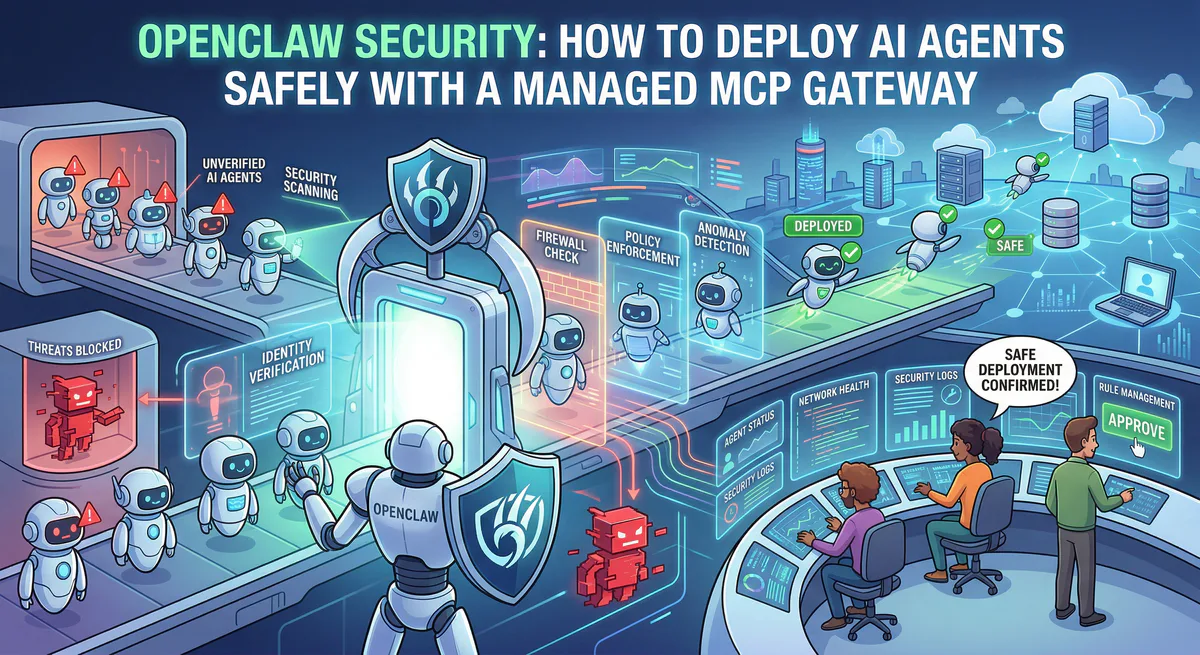
What we do well. We built Vinkius as an MCP-first platform from the ground up. Every tool call — regardless of which agent makes it or which server it targets — passes through our managed gateway. This gives us a unique execution layer that no other platform in this comparison provides:
Our semantic intent classification inspects every tool call and categorizes it by verb type — QUERY, MODIFY, or DESTRUCTIVE — before execution. If your compliance policy says agents cannot perform destructive mutations without explicit approval, we enforce that at the edge. Not at the prompt level. At the execution level.
Our DLP pipeline operates on outbound payloads, not just inbound prompts. If a compromised agent attempts to exfiltrate a .env file, an SSH key, or PII through a tool call to any downstream server, our DLP catches it and kills the request before the data leaves the perimeter. This is the critical difference between prompt-level anonymization and true data exfiltration prevention.
Our cryptographic audit trail hash-chains every execution record, creating an immutable, forensic-grade log that cannot be altered after the fact. For SOC 2 auditors and compliance teams, this is the difference between “we log agent actions” and “we can cryptographically prove exactly what happened.”
Our marketplace is open. Third-party developers can publish, price, and sell MCP servers directly on the platform. This means our catalog grows organically — and the developers building servers have economic incentive to maintain them.
We also provide an emergency kill switch that revokes all active tokens, terminates all connections, and locks any server to inactive state with one click. When an incident happens at 3 AM, you need a single button, not a terminal session.
Where we fall short. We are newer to market than Composio. Their SOC 2 Type II certification predates ours. Their integration library was built over a longer period, which means some niche SaaS connectors exist on Composio that have not yet been published on our marketplace. We are smaller, which means our support response times can be slower during peak periods. And our pricing model — while competitive — does not offer a permanent free tier for high-volume usage.
Best for: Teams that need a production-grade MCP gateway with real DLP, semantic governance, cryptographic audit logging, and an open marketplace — particularly those deploying agents in regulated industries or handling sensitive data.
The Decision Framework
Rather than telling you to pick us, here’s how to think about the decision:
If you need maximum breadth with minimal engineering effort — and you’re already a Zapier customer — start there. You’ll trade depth and governance for speed.
If you’re prototyping and exploring the MCP ecosystem — Smithery is the best starting point. Browse, install, experiment.
If you need enterprise-grade auth and a large pre-built integration library — evaluate Composio. Their SOC 2 Type II certification and managed OAuth flows are battle-tested.
If you need an execution firewall — a governed gateway that inspects, classifies, and audits every agent action with real DLP and semantic classification — that’s what we built. Explore our infrastructure →
Every platform in this list is solving a real problem. The question is which layer of the stack matters most for your deployment.
See Vinkius in action. Browse the App Catalog to explore governed MCP servers, or create a free account and connect your first server in under two minutes.
Your agents need tools. We make them safe.
Pick an MCP server from the catalog. Subscribe. Copy the URL. Paste it into Claude, Cursor, or any client. One URL — DLP, audit trail, and kill switch included.
V8 sandbox isolation · Semantic DLP · Cryptographic audit trail · Emergency kill switch