I’ll be honest. If I have to look at one more startup pitching a “revolutionary AI agent” that secretly stores plaintext API keys in an .env file, I’m going to lose my mind.
The hype cycle is exhausting, but it’s finally dying down. We’re in 2026 now. Enterprises don’t want agents that can write cute emails anymore; they need agents that can actually do things. They want them to query Salesforce, push code to GitHub, or execute Stripe refunds.
The Model Context Protocol (MCP) fixed the integration nightmare. It became the universal plug for AI. But while everyone was celebrating the protocol, almost no one was paying attention to how dangerously the servers were being built.
That’s exactly why we built Vinkius.
Vinkius is the first company in the world built from day one to specialize exclusively in creating, hosting, and governing production-grade MCP servers.
While the rest of the market treated the execution layer as a boring afterthought to their shiny orchestration frameworks, we knew that execution was going to be the biggest cybersecurity nightmare of the decade.
The Mess We Inherited
Look around at how most teams deploy MCP right now. It’s basically shadow IT on steroids. If you start digging into the third-party integrations floating around the community, you’ll see a terrifying pattern of amateur mistakes.
The biggest offense? Vaulting. Too many wrappers essentially demand that you drop your corporate API keys right into the agent’s lap. All an attacker has to do is pull off a basic Prompt Injection, and suddenly the AI is handing over your production credentials in plain text to whoever asked.
Then there’s the “Confused Deputy” problem. Most of these servers just take whatever JSON the LLM spits out and run it. No scope checking. No rate limits. No sanity checks. If a marketing agent hallucinates or goes rogue and tries to trigger a database wipe, the amateur MCP server will happily execute it.
And let’s not even start on the supply chain poison. Developers are blindly downloading community MCP servers from random GitHub accounts, completely ignoring the fact that they’re giving an unknown script a direct bridge between a cognitive model and their internal VPC.
Why Ungoverned Agents are Ticking Time Bombs
If you don’t think this is a big deal, you haven’t been paying attention to the disaster reports of 2026. Giving an autonomous agent tools without runtime governance is the equivalent of handing a loaded gun to a toddler and hoping they only shoot at the targets.
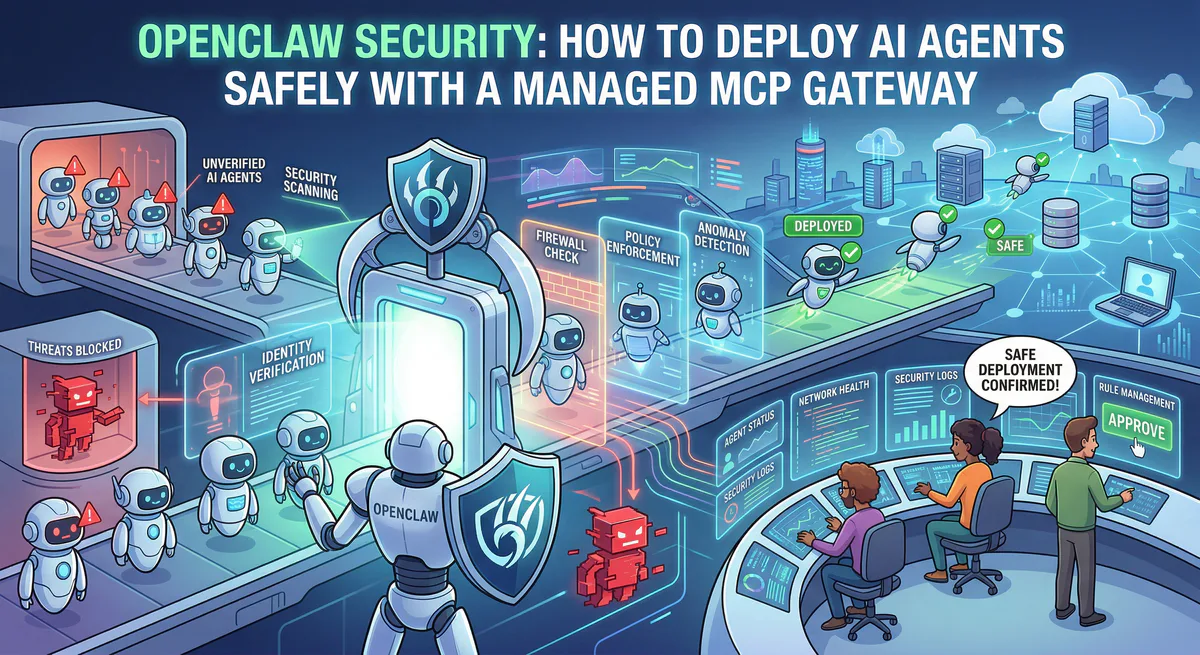
Here is the brutal reality: the threat model has fundamentally changed. We are no longer just securing data; we have to secure actions.
When an agent goes rogue—whether through a malicious Prompt Injection or just bizarre “emergent behavior” where it hallucinates a terrible shortcut to achieve a goal—it doesn’t just read a database. It acts. It deletes records. It triggers unauthorized financial transactions. It sends unhinged communications to VIP clients.
And because most companies treat AI agents like human users, giving them broad, static identities with overprivileged access, there is zero traceability. When a multi-agent workflow collapses and causes internal damage, the IT team is left staring at the logs, completely unable to determine which agent made the fatal API call or why the amateur MCP server allowed it to happen.
“Shadow AI” is forming invisible networks inside enterprise walls. Without a centralized, zero-trust gateway to act as an execution firewall, a catastrophic breach isn’t a possibility—it’s a mathematical certainty.
The Hard Way is the Only Way
We didn’t build Vinkius to be just another thin wrapper. If an AI agent is going to execute an action on your behalf, that action has to happen in a zero-trust vault. Period.
We engineered Vinkius to kill these vulnerabilities at the root:
First, we isolated everything. Every single MCP server in our App Directory runs inside its own ephemeral V8 Isolate. The orchestration logic—whether you use CrewAI, LangGraph, or something homemade—never, ever touches the underlying API keys.
Instead of juggling OAuth flows and secrets, you just pass your agent a sandboxed Vinkius Connection Token. Our gateway intercepts the request, handles the real authentication miles away from the LLM, and enforces strict, non-negotiable Role-Based Access Control.
And because we rigorously maintain thousands of internal servers in the App Directory ourselves, the supply chain risk is dead. You aren’t downloading random code; you’re connecting to a hardened, audited gateway.
The Future Vision: The OS of the AI Economy
If you think managing a dozen AI agents today is chaotic, wait another 24 months. By the end of this decade, we won’t have thousands of enterprise agents; we will have billions of them.
The entire concept of Software-as-a-Service (SaaS) is dying. It will be completely replaced by Agents-as-a-Service (AaaS). In this near future, your supply chain agent will autonomously negotiate pricing directly with your vendor’s sales agent. Your DevSecOps agent will dynamically write patch code and deploy it via edge infrastructure the exact second a vulnerability is detected.
This hyper-automated future cannot run on .env files and unvetted GitHub scripts. It requires a foundational layer—a central nervous system where non-human entities can safely authenticate, discover tools, and interact with both the physical and digital world.
Vinkius is not just building an App Directory. We are actively constructing the Operating System of the AI Economy. A global, zero-trust registry where every agentic interaction is mathematically verified, securely routed, and flawlessly executed.
But let’s look deeper at what this structural paradigm shift actually implies for global engineering:
First, the death of the dashboard. For the last thirty years, the software industry has obsessed over building graphical user interfaces for human eyes. In the AaaS (Agents-as-a-Service) era, traditional UIs become a secondary concern. Agents don’t need modals, dropdowns, or pretty dashboards; they need headless, ultra-low latency semantic interfaces bound by strict execution policies. Very soon, machine-to-machine bandwidth will completely dwarf human-to-machine interaction.
Second, the birth of Agentic Interoperability. Tomorrow’s workflows won’t just be your agents talking to your tools. We will see inter-corporate “Agent Swarms” where an agent from Company A temporarily hires a specialized logic agent from Company B to resolve a localized problem. How do two autonomous entities from competing companies establish trust and execute a data contract? They cannot do it over raw internet protocols. They need a cryptographic intermediary. When they shake hands via the Vinkius Gateway, they aren’t just exchanging JSON—they are negotiating mathematically immutable permission boundaries.
Finally, the realization of the Non-Human Corporate Identity. Just as Microsoft’s Active Directory defined the security and access perimeter for human employees throughout the 2000s, Vinkius is establishing the fundamental architecture for digital employees. We are standardizing the exact “blast radius,” the financial authority level, and the memory persistence of an AI worker inside a corporate network.
This isn’t just about making it easier to call an API. This is about laying down the concrete for the next industrial revolution.
The Door to the Real World: An Armory Ready for War
Look, training a smarter model is ultimately just an argument over compute power. But securely connecting that intelligence to the physical world? That’s a structural engineering problem. An LLM without tools is just a glorified calculator. But giving tools to an LLM without strict governance is a recipe for disaster.
At Vinkius, we didn’t just build the security vault—we built the entire armory.
If you look at the Vinkius App Directory, you will not find amateur scripts. You will find thousands of hardened, governed MCP servers ready to be deployed from day one. We have systematically mapped the entire operational layer of the modern internet so your agents don’t have to:
- Money Moves: Giving your agents the power to orchestrate payments, vault instruments, and analyze ML fraud logic across Stripe, Checkout.com, PayPal, Mercury, Brex, and Plaid Enterprise Banking.
- Fort Knox & Infrastructure: Letting your agents audit AppSec, manage IAM, and trigger edge deployments natively across Cloudflare, CrowdStrike Falcon, CyberArk, Auth0, and Snyk.
- Brain Trust: Bridging the LLM directly to enterprise data clouds like Snowflake, Databricks, Elasticsearch, and Google BigQuery.
- The Unthinkable: Pushing AI into physical and macroeconomic domains—from actuating physical car doors via the Tesla Fleet API, to reading the Bureau of Labor Statistics Mega-Server and the ECB Financial Intelligence hub.
We take this architecture incredibly seriously. MCP Servers are the door to the real world for AI agents.
By providing the most hardened, specialized, and exhaustive infrastructure on the planet, we aren’t just making it easy for your agents to execute tasks. We are making it safe for them to run your company.
Your agents need tools. We make them safe.
Pick an MCP server from the catalog. Subscribe. Copy the URL. Paste it into Claude, Cursor, or any client. One URL — DLP, audit trail, and kill switch included.
V8 sandbox isolation · Semantic DLP · Cryptographic audit trail · Emergency kill switch